Project 2 Reference: Entanglement, BSM, and Teleportation
Project Discoveries, Visualizing Entanglement and Teleportation
Let’s begin by visualizing the project process with a guided description to understand the concepts behind the code. The following flowcharts provide a more tangible representation of the process. In Part A, we observe how entanglement and measurement are established, laying a foundation for these concepts. In Part B, we extend this process to illustrate how teleportation works physically and how it could occur over a network, transmitting both classical data and qubits.
Let’s review the requirements for a Bell State Measurement (BSM), which is a quantum measurement procedure. Three conditions must be met:
- Superposition: At least one qubit must be in superposition to allow the system to access multiple states simultaneously, which is necessary for entanglement.
- Entanglement: The two qubits must be entangled via a gate operation, such as a CNOT, to create correlations between their states.
- Measurement alignment: An additional gate operation is applied to map the Bell basis to the computational basis, enabling classical measurement of the entangled qubits.
Let’s begin with Part A of Project 2 below, where we conducted the BSM alone without incorporating teleportation.
Part A – Entanglement and BSM [Bell State Measurement]
In the flowchart below, you can follow the conceptual process of entanglement from start to finish. Note that entanglement is a physical phenomenon and can be achieved in multiple ways using different multi-qubit gates; it is not a fixed process like a protocol.
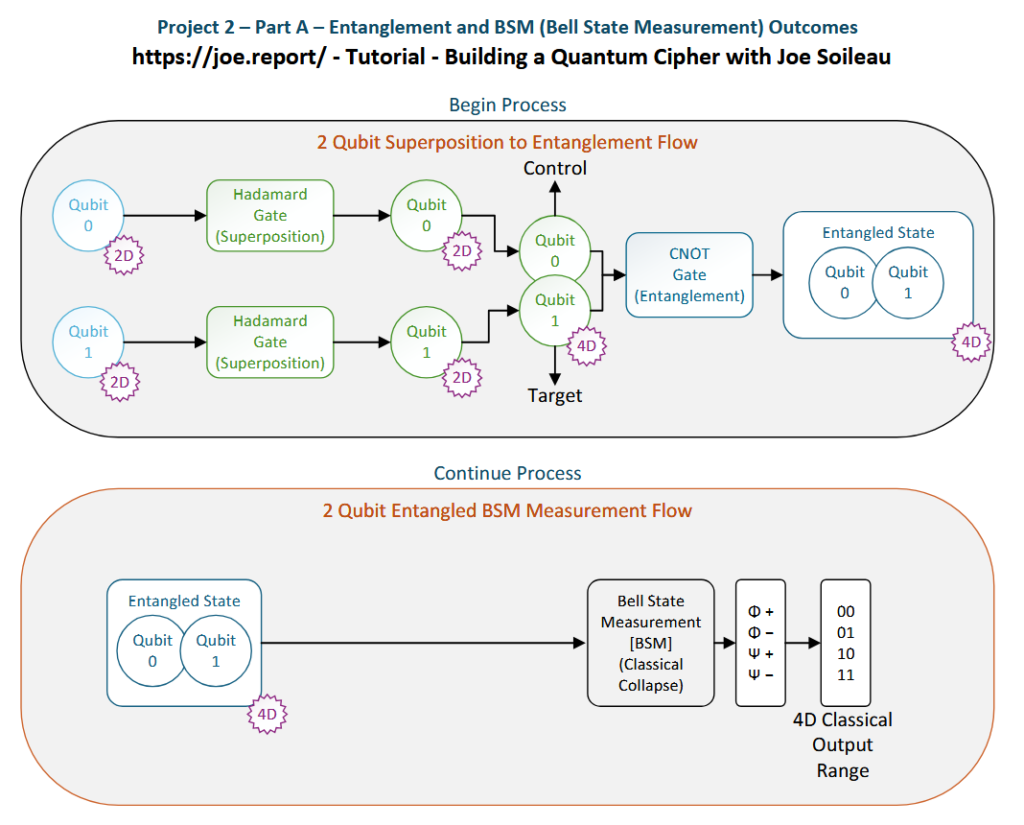
Programming Relationship to Process Flow:
- We created two qubits (Q0, Q1) and two classical bits (C0, C1) when we initialized our quantum circuit in Qiskit.
- Both Q0 and Q1 were passed through Hadamard gates, placing each qubit into superposition. Placing both qubits into superposition allows the system to access all four possible Bell-state measurement outcomes upon collapse. If only one qubit were placed into superposition, the measurement results would be limited to two possible classical outcomes. This configuration was chosen to illustrate the full range of Bell-state correlations. It should be noted that it is not required for both qubits to pass through Hadamard gates to perform entanglement or a BSM; using only one qubit in superposition would still work but would yield only two possible outcomes.
- After Q0 and Q1 were placed in superposition, they were passed through a CNOT gate, with Q0 as the control qubit and Q1 as the target. The CNOT operates conditionally, applying a transformation to the target qubit based on the state of the control qubit. Because the control qubit is in superposition, this conditional operation establishes a correlated quantum state between the two qubits, resulting in entanglement.
- Once entanglement is established, a Bell State Measurement is performed, collapsing the joint quantum state into one of four possible Bell states. The circuit was executed over 1,024 shots, and the resulting classical outcomes were plotted as histograms to visualize the Bell-state correlations.
Part B – Entanglement, Teleportation and BSM [Bell State Measurement]
In contrast to the process of entanglement, teleportation itself is a protocol. This means it has strict requirements that must be met in order for it to function.
The protocol requirements that must be met for teleportation are:
- Shared entangled pair: A pair of qubits must be entangled and distributed between the sender and receiver.
- Bell State Measurement (BSM): The sender performs a BSM on their qubits to project them onto the Bell basis.
- Classical communication: The measurement results are transmitted classically to the receiver, who applies the necessary operations to reconstruct the original quantum state.
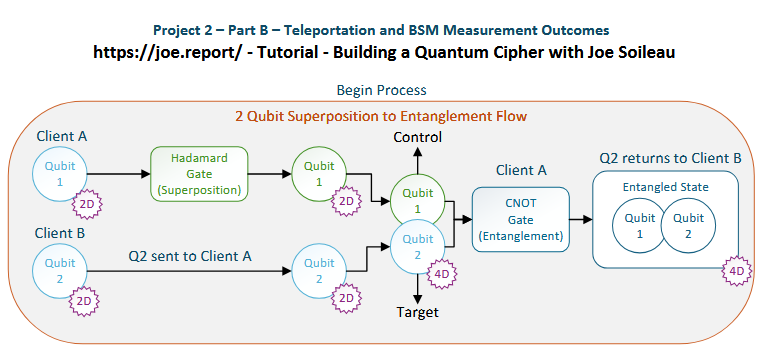
The main programming differences are:
- We initialized three qubits (Q0, Q1, Q2) instead of two, to accommodate a messenger qubit for the teleportation protocol, and
- Only Q1 was placed into superposition before the initial entanglement.
What differs more is the physical flow behind the code.
Q1 originates at Client A
Q2 originates at Client B
Q0 originates at Client A
So, Q2 originates at a separate location and is physically transported to meet Q1, because, in this scenario, entanglement requires physical proximity.
Keeping this in mind, Q1 and Q2 are created at different locations and moved to interact, where the physics of entanglement occurs on the tangible qubits themselves. In practice, these qubits could be attached to photons or another stabilized transmission medium over a quantum-capable network. Understanding this physical flow will help clarify the networking diagram and demonstrate how teleportation functions in experimental lab setups capable of qubit transmission.
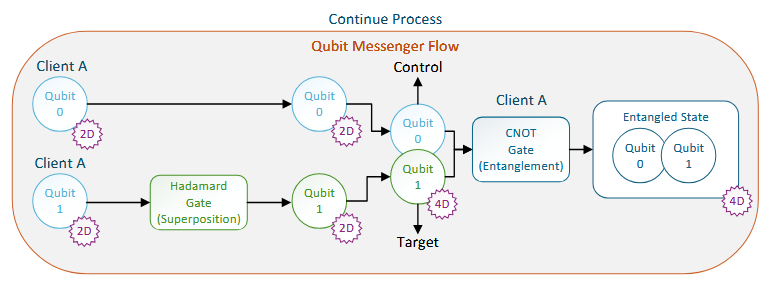
Above is where the process flow begins to diverge from Part A.
Remember: Q2 has already been entangled with Q1 and then returned to its origin at Client B. At this point, Q1 is still physically present on its side of the network, and it is already correlated with Q2. Q0 is introduced as the messenger qubit, located at Client A with Q1. Q1 is passed through a Hadamard gate again to enter superposition, and then Q0 and Q1 are entangled via a CNOT gate.
You may be wondering why Q1 has to be placed into superposition yet again before being entangled with Q0, since it was already placed into superposition before entanglement with Q2. The reason is because the basis of entanglement between Q1:Q2 and Q1:Q0 must be distinct. This is due to how the CNOT gate functions: it creates entanglement between one control and one target qubit, establishing correlations specific to that pair. Therefore, Q1 is placed into superposition relative to Q0 to correctly establish entanglement, just as it was previously with Q2.
At this stage, Q1 is simultaneously entangled with both Q0 and Q2. However, Q2 cannot directly “know” its updated correlation with the combined Q0–Q1 system. To transmit this information, the Bell State Measurement (BSM) results from Q0 are sent classically to Q2. Using this classical information, Q2 can correctly reconstruct its part of the quantum correlation, effectively receiving the teleported state from the Q0–Q1 interaction.
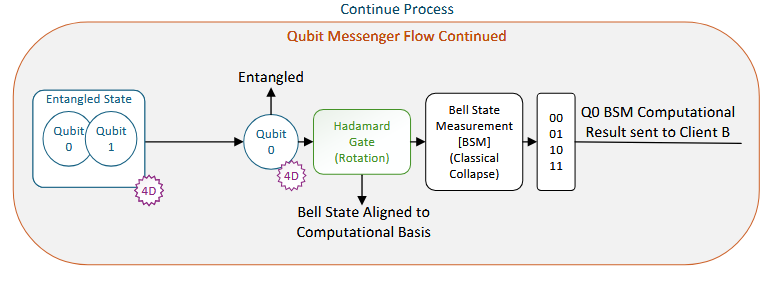
Above is the process when the messenger qubit’s BSM is performed. Q0, physically separated from Q1, is passed through a Hadamard gate to align the Bell basis with the computational basis, which is necessary to perform the BSM.
Next, Q0’s BSM result is sent to the Client B location of Q2 below.
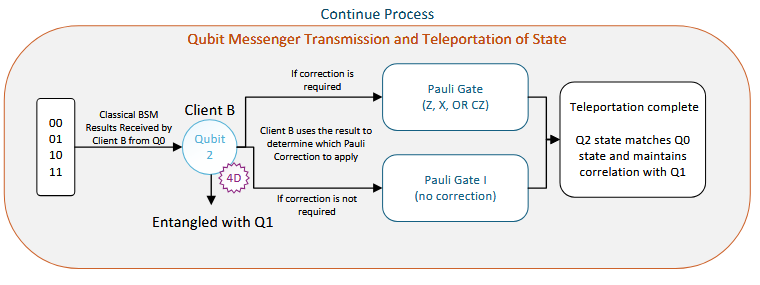
Client B receives the classical information from Q0 (the messenger qubit) and applies the appropriate Pauli corrections to Q2. This adjusts Q2’s state to match the intended quantum state from the Q0–Q1 system, effectively teleporting the quantum information to Client B and implementing it locally.
Entanglement, BSM, and Teleportation in reality
Now that we understand the programming and process flows of teleportation, as well as their general physical interactions, we can focus on the physical networking layer and the requirements for the protocol to function. While some aspects were mentioned earlier, this diagram focuses specifically on the networking process itself:
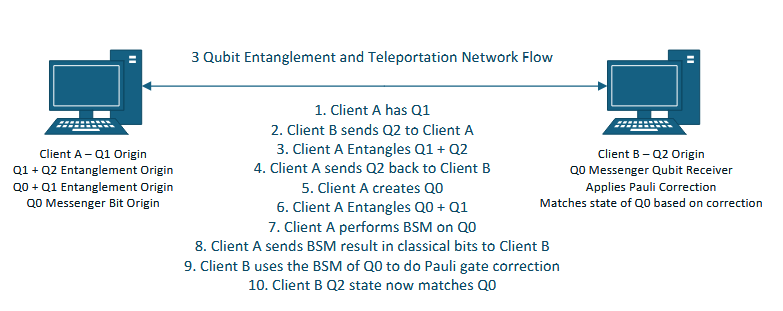
Above, you can clearly see how the physical transmission occurs, following the step-by-step process from a networking perspective.
In reality, however, there are variables that can impact this process, and the technology required for teleportation is not yet widely available. Next, we will examine some of these limitations and the reasons behind them.
Noise, Decoherence, and Error sources
Noise: Quantum systems are extremely sensitive to their environment. Random fluctuations, electromagnetic interference, or thermal effects can disturb qubits, causing their states to drift and introducing errors into entanglement and teleportation processes.
Decoherence: Over time, qubits naturally lose their quantum information due to interactions with the environment. This decay limits how long entangled states can be reliably maintained, restricting teleportation over long distances or extended operations.
Gate errors: Quantum gates, like Hadamard or CNOT, are not perfect in real systems. Small imperfections accumulate over multiple operations, which can degrade the fidelity of entanglement and teleportation outcomes.
Measurement errors: Performing a Bell State Measurement (BSM) or other qubit measurements can be imperfect. Even minor inaccuracies in reading qubit states can lead to incorrect Pauli corrections and failed teleportation.
Timing/Synchronization issues: Teleportation requires precise coordination between qubit operations and classical communication. Any mismatch in timing can disrupt the protocol, causing errors in the reconstructed quantum state.
Photon loss/Transmission errors: When qubits are transmitted, often via photons in quantum networks, some may be lost or corrupted along the way. Losses reduce the reliability of teleportation, especially over longer distances.
Crosstalk: In multi-qubit systems, qubits may unintentionally interact with nearby qubits, leading to errors in entanglement and state evolution. Crosstalk can reduce the overall fidelity of the teleportation protocol.
Even though these factors are outside the scope of the experiments in this project, it is important to keep current limitations in mind. There are dedicated teams working to reduce these barriers and make quantum communications more reliable. However, teleportation has not yet been achieved outside highly controlled lab environments or specialized networks. That doesn’t mean that the developmental frameworks and experimentation should be abandoned, however, because they can be implemented quickly once things become streamlined.
Experiments and learning like this can also help us prepare in advance to protect against potential quantum security exploits in the future.
Teleportation Material and Physical considerations
There are multiple technologies and materials which are already being used to complete teleportation:
- Photons over Fiber-Optic Networks (longest distance)
- Photonic Chip-to-Chip Teleportation (limited range)
- Hybrid Photon-Matter Interfaces (short range nodes)
- Distant Matter Qubit Systems (localized)
- Deterministic Teleportation in Optical Setups (short range)
However, only photon-based transmission over fiber-optic (or free-space) networks currently enables teleportation across practical distances, making it the most viable approach for real-world, networked applications such as quantum key distribution (QKD) and applied cryptography.
So, what are the physical considerations we have to be aware of with photon-based transmission over fiber-optics?
- Photon loss / attenuation: Photons are absorbed or scattered as they travel, reducing the probability of successful entanglement and teleportation.
- Dispersion: Different photon wavelengths travel at slightly different speeds, stretching pulses and affecting timing and interference.
- Fiber length limits and repeaters: Even low-loss fiber can only carry entangled photons so far before a quantum repeater or node is needed.
- Temperature and mechanical stress: Environmental changes can subtly change fiber properties, shifting polarization or phase.
- Connector and splice losses: Every joint or connector in a fiber link introduces small but cumulative loss.
- Photon source stability: Imperfect or drifting sources reduce entanglement fidelity.
- Channel multiplexing effects: If quantum and classical signals share fiber, they can interfere with each other.
However, as noted above, these physical limitations should not discourage the development of quantum protocols or cryptography architectures. Once the infrastructure is in place, these systems can be implemented immediately. This is why we can confidently expand on teleportation and introduce entanglement swapping as an adjacent concept or extension of the teleportation protocol, particularly for use in quantum security.
Combining Concepts: Entanglement Swapping and Teleportation
Having introduced teleportation, we can now briefly expand on how entanglement swapping builds on these principles, allowing entanglement to be shared between qubits that have never directly interacted. This concept is key for extending teleportation across larger networks and for future quantum communication systems.
So, what does entanglement swapping do exactly? It’s a process that transfers quantum states across qubits without requiring those qubits to ever physically interact. It typically uses a Bell State Measurement (BSM) and principles of teleportation for single-qubit entangled states. However, entanglement swapping can also be applied to multi-qubit states, like GHZ (Greenberger–Horne–Zeilinger) and W states.
However, we don’t need to go too in-depth with these concepts just yet.
We will continue to delve more into entanglement swapping and multi-qubit systems in later parts of the tutorial series, because it is going to be an important basis for later projects and experimentation. For now, we will focus on what we can incorporate with single-qubit entanglement and teleportation. We will soon discover how to combine operations, protocols and algorithms to create unique quantum outcomes.
Combining Operators, Protocols, and Algorithms
Now that we’ve explored entanglement, teleportation, and the briefly touched on the concept of entanglement swapping, we can turn our attention to combining quantum operators with algorithms. This allows us to create structured quantum workflows, manipulate qubits in more complex ways, and achieve specific computational outcomes.
So what is a quantum algorithm?
A quantum algorithm is a set of instructions designed to run on a quantum computer, using qubits and quantum operations to solve problems. Unlike classical algorithms, which operate on bits that are either 0 or 1, quantum algorithms can leverage superposition, entanglement, and interference to perform computations in ways that are often more efficient or fundamentally different from classical approaches.
Quantum-adjacent algorithms?
We can’t talk about quantum algorithms without mentioning PQC algorithms. However, PQC (Post Quantum Computing) algorithms are not quantum. They are, however, classical algorithms that are designed to remain secure against future attacks from quantum computers. Some PQC algorithms are: (Kyber, FrodoKEM, NTRU, Dilithium, Falcon, Saber). They use advanced mathematical structures that are designed to be resistant to future quantum computing attacks.
When working with quantum algorithms, the landscape changes, because we can leverage the physical properties of qubits to gain advantages in processing information, as demonstrated by algorithms like Grover’s.
In Part 4 of Building a Quantum Cipher, we will explore different types of quantum algorithms and examine how they interact within a quantum framework, enabling us to accomplish tasks in ways that differ from classical computing.
References
Northwestern Engineers Achieve Quantum Teleportation Over Existing Internet Cable, Dec 2024 https://thequantuminsider.com/2024/12/27/northwestern-engineers-achieve-quantum-teleportation-over-existing-internet-cable
Chip-to-chip photonic quantum teleportation over optical fibers of 12.3 km, July 2025 https://www.nature.com/articles/s41377-025-01920-z
Deterministic quantum teleportation of a path-encoded state using entangled photons, November 2025 https://link.springer.com/article/10.1140/epjqt/s40507-025-00434-2
Leave a Reply